When it comes to protecting your IT assets and providing intelligent security analytics at the cloud scale for your enterprise, Microsoft Sentinel is an excellent choice for you to use in your cloud environment. Over the next few blogs I write, I will go in-depth with Microsoft Sentinel and why it can benefit your business and go over different examples of how you would deploy this in a production environment.
What Is Microsoft Sentinel?
Microsoft Sentinel (formally Azure Sentinel) is a SIEM (Security Information and Event Management) and SOAR (Security Information and Event Management) tool, and it is Microsoft’s cloud-native SIEM and SOAR solution that you can deploy in your Azure tenant via the Azure portal. Once you have deployed Microsoft Sentinel, it will immediately align with your pre-existing organizational policies. In addition, Microsoft Sentinel will assist you with data normalization, compliance, threat detection, security alerting, and many more security-rich features to help ensure your cloud environment meets your security needs.
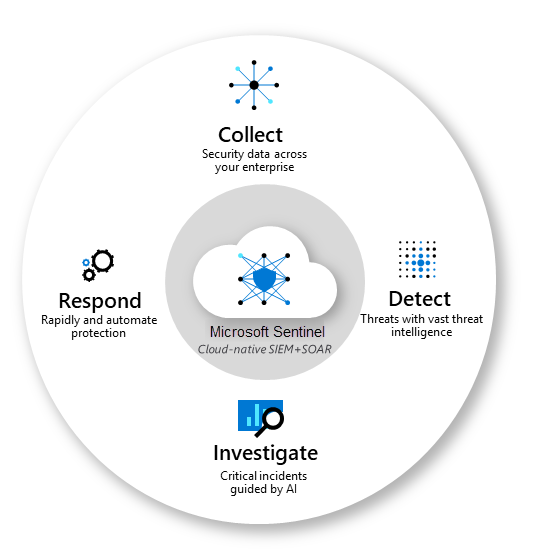
At a high level, this is how Microsoft Sentinel works:
- Collects data across all users, devices, applications, and infrastructure, on-premises and in multiple clouds
- Uses Microsoft’s analytics and threat intelligence to detect previously undetected threats and minimize false positives
- Investigates threats using artificial intelligence to hunt for suspicious activities at scale
- Responds to incidents with built-in orchestration and automation for tasks
Source: What is Microsoft Sentinel? | Microsoft Learn
Data Connectors
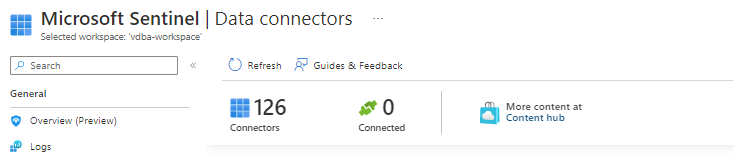
Before you can do anything with Microsoft Sentinel, you will need to connect your data sources. At this moment, Microsoft Sentinel has around 126 different data connectors you can use, but they are constantly evolving as time goes on.
Suppose you already use Microsoft native solutions like Microsoft 365 Defender, Microsoft Defender for Cloud, Office 365, Microsoft Defender for IoT, and Azure service sources like Azure Active Directory. In that case, you can ingest this data through Microsoft Sentinel by setting up the Data Connector. This can provide a unified experience for gathering your data sources within the Microsoft product ecosystem.
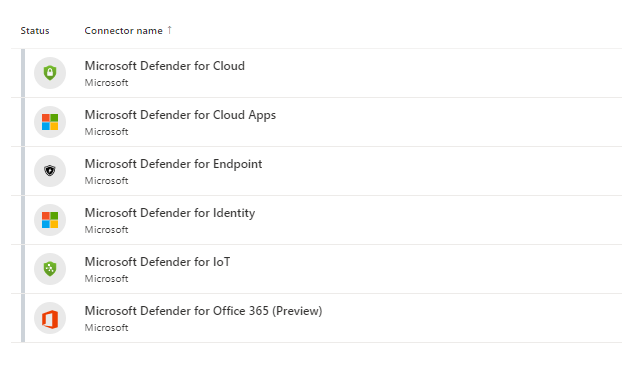
If you need data ingested from third-party sources like AWS, Google Cloud, etc., there are connectors for those as well, and as I previously mentioned above, Microsoft is continuing to add new data connectors all the time as time evolves. In one of my real-world examples, I have used Microsoft Sentinel to ingest data from one of my Palo Alto Networks, and it allowed me to have a centralized place to view dashboards, create custom alerts, and improve investigations.
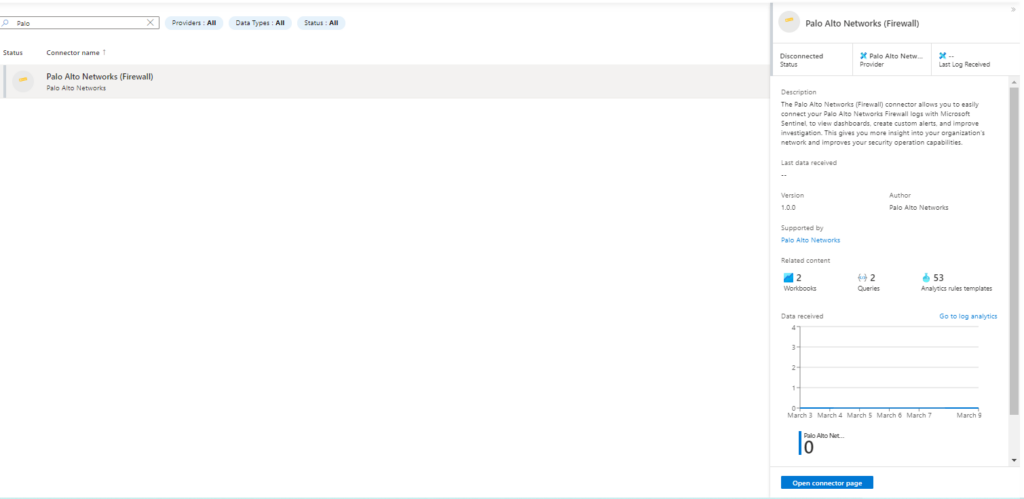
This Palo Alto-specific data connector also came with already predefined workbooks, queries, and analytics I could use without building custom ones.

As mentioned above in my upcoming blogs I will go into more detail about deploying these data connectors and ingesting real data and using it to benefit your organization.
What Are Workbooks?
Microsoft Sentinel Workbooks helps you reduce noise and minimize the number of alerts that may come up that need to be reviewed and investigated, as it uses analytics to correlate these alerts into incidents. You may be used to working with Workbooks in Azure Monitor, but they display differently when using Workbooks in Microsoft Sentinel. You can also create custom workbooks to use across the data you have ingested, and Microsoft Sentinel comes with built-in workbook templates to allow you to quickly gain insights across your data once you connect a data source.
Hunting For Threats
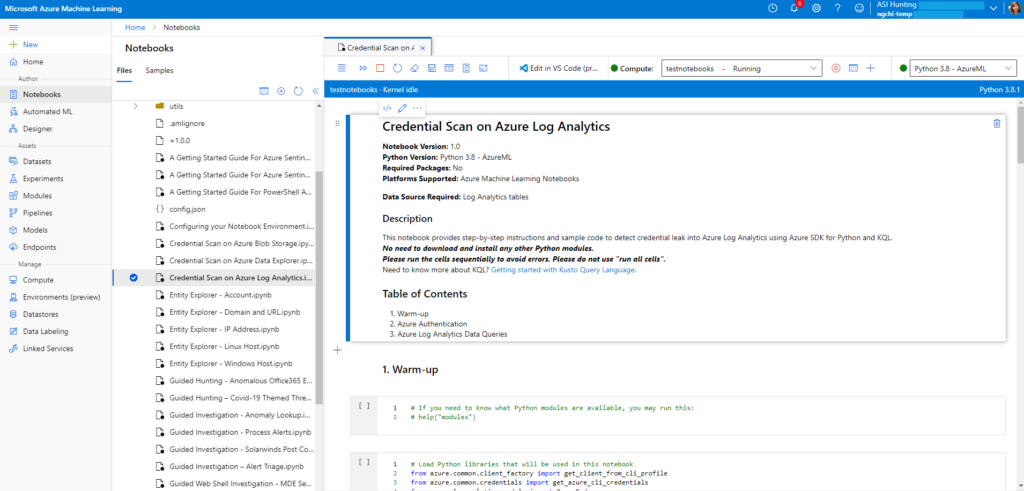
Microsoft Sentinel has powerful built-in hunting search-and-query tools based on the MITRE framework, which enables you to proactively hunt for security threats across the data sources in your organization before alerts are triggered. You can create custom detection rules based on your queries and use insights as alerts to security incident responders. When you are hunting, Microsoft Sentinel allows you to create bookmarks, enabling you to leave a solid placeholder for when you need to return at a later time. You can also enhance your threat hunting with notebooks, as Microsoft Sentinel supports Jupyter notebooks in Azure Machine Learning workspaces, including full libraries for machine learning, visualization, and data analysis.
Source: What is Microsoft Sentinel? | Microsoft Learn
Syslog and Common Event Format (CEF)
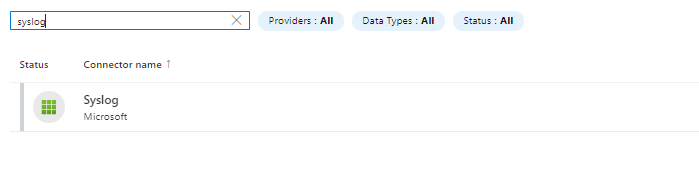
For Linux-based, Syslog-supporting devices, you can use Microsoft Sentinel to ingest these logs using the Log Analytics agent for Linux, formerly known as the OMS agent.
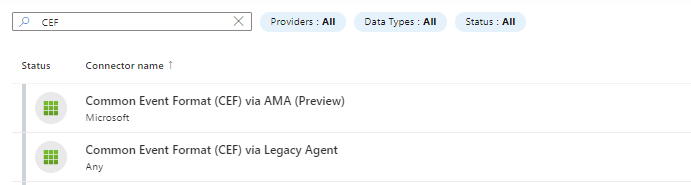
Log formats can vary, but many sources will support CEF-based formatting, and the Microsoft Sentinel agent, the log analytics agent, converts the CEF-formatted logs into a format that the Log Analytics agent can ingest.
Source: Microsoft Sentinel data connectors | Microsoft Learn
Syslog Data Connector
CEF Data Connectors
Download Security Content From The Community
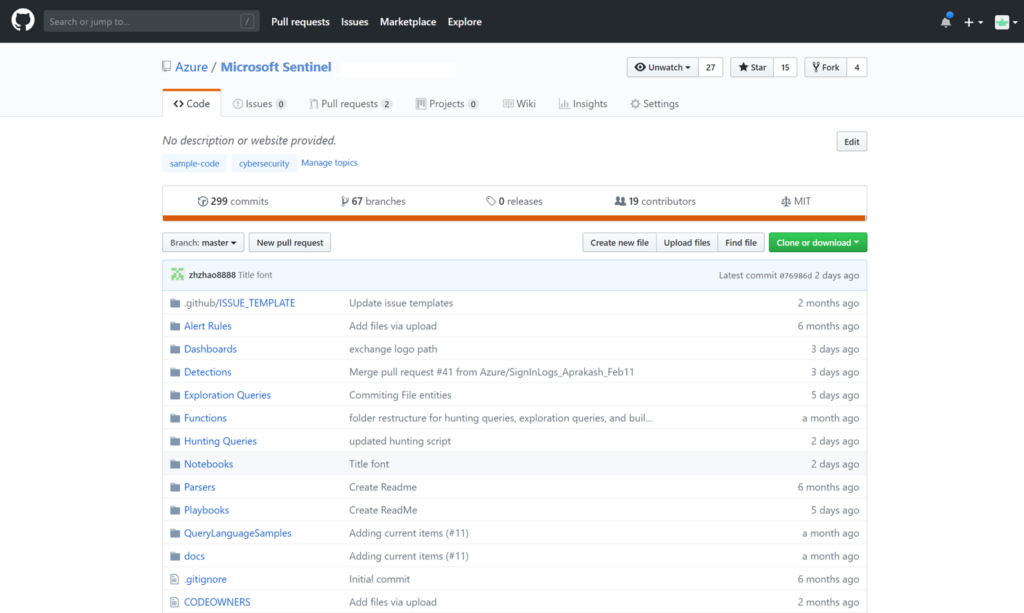
The Microsoft Sentinel community is an excellent resource for threat detection and automation. Microsoft security analysts create and add new workbooks, hunting queries, and more for you to use within your environment all the time. You can download and sample content from the private community GitHub repository here.
Source: What is Microsoft Sentinel? | Microsoft Learn
I look forward to going more in-depth in my upcoming blogs over Microsoft Sentinel to help your organization enhance its cloud security posture. If you have any questions or are ever needing assistance, please reach out to us at XTIVIA.